Business LOG Server
Monitors and records corporate IT logs, facilitating regulatory compliance. It offers analysis, audits, advanced reporting, real-time monitoring, cloud backup and centralized management, improving transparency and data protection.
COMPLIANCE AND SECURITY
Thanks to Business LOG, everything is under control.
Hosts and services control
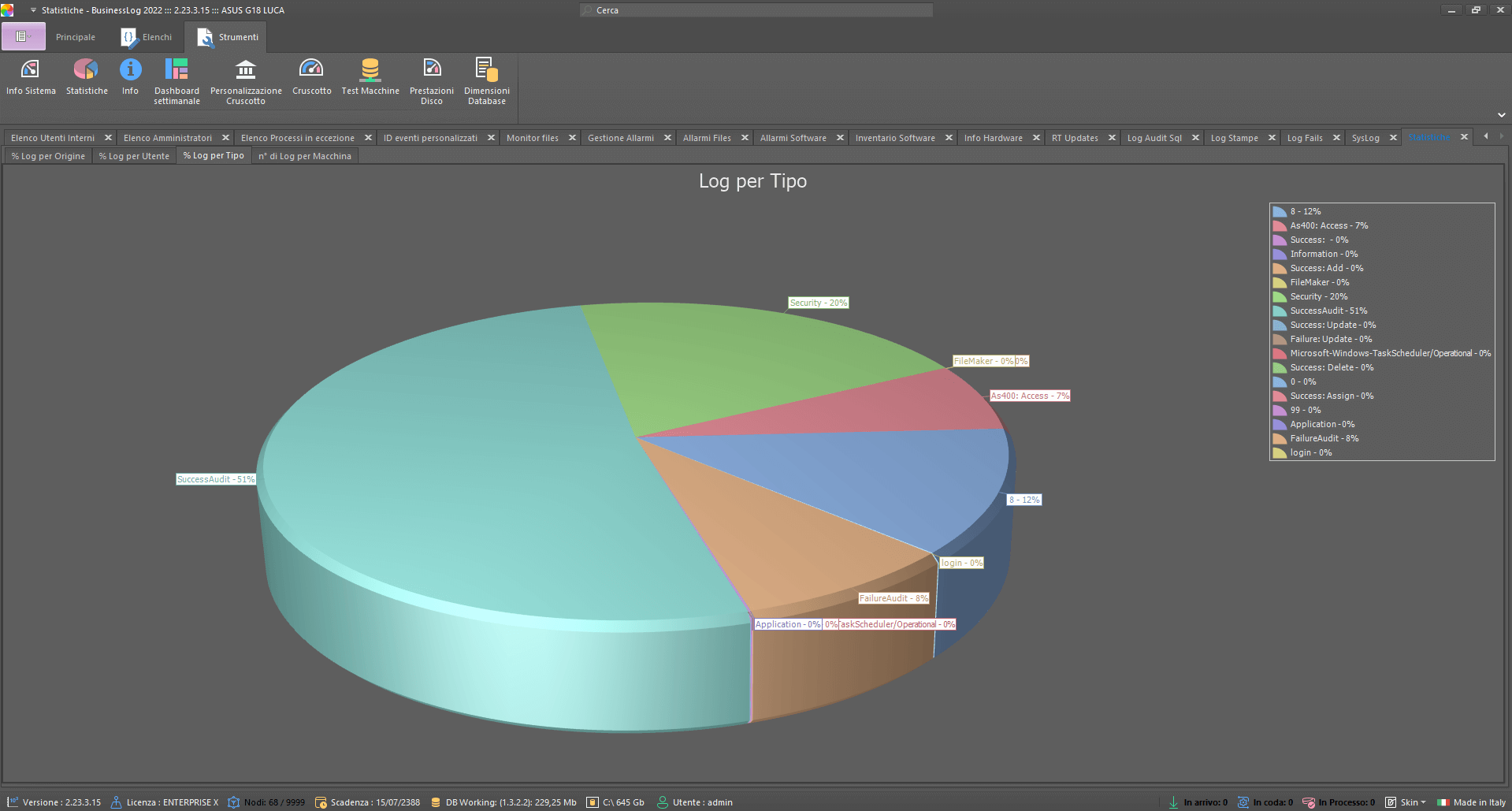
Analytics and reporting
Secured log collection
Regulatory compliance
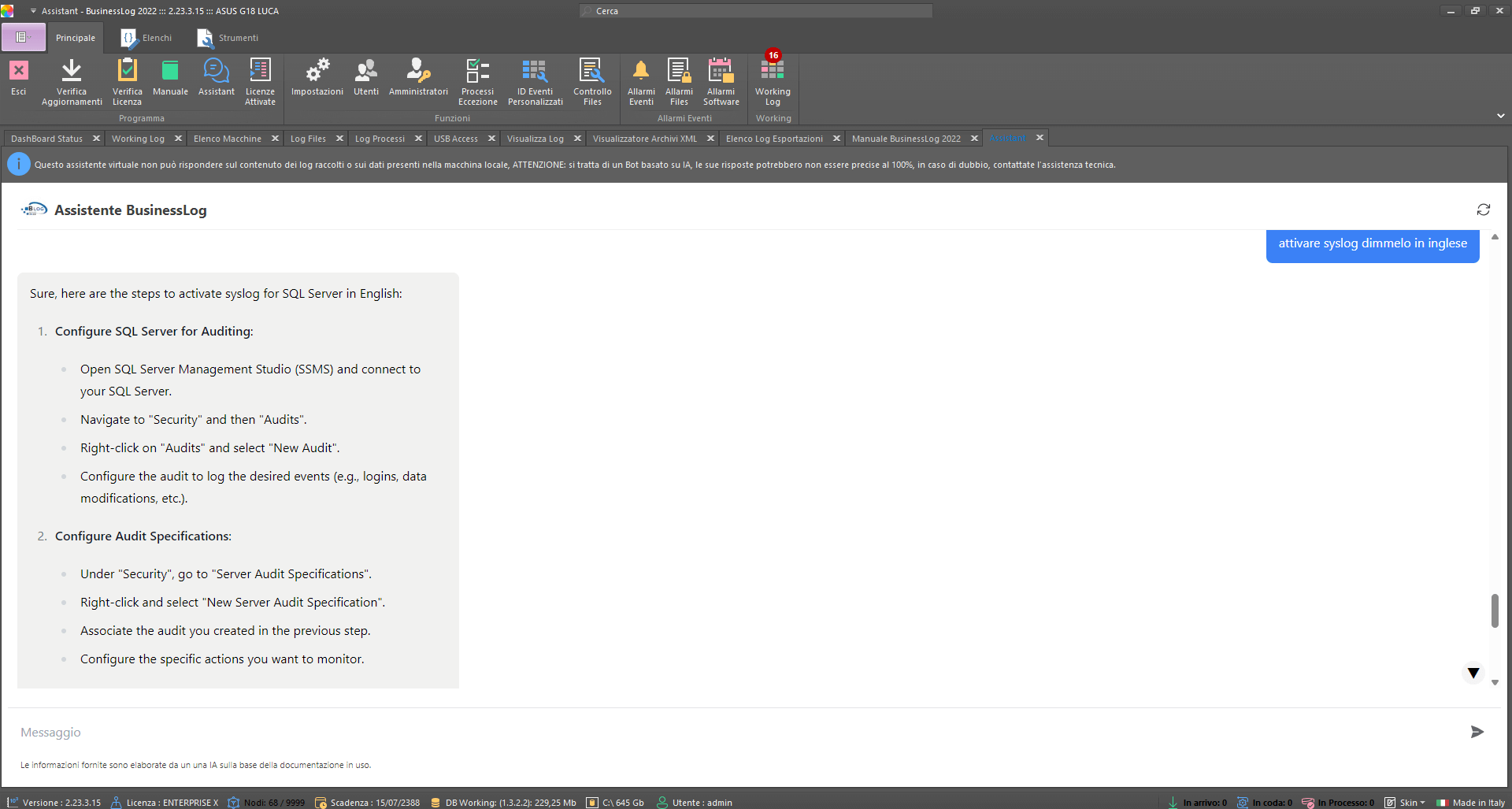
Artificial Intelligence
The integration of AI into Business LOG represents a significant advancement in enterprise log management. Through predictive analytics, response automation and compliance optimization, AI makes log management more efficient, secure and proactive, delivering invaluable value to modern organizations.
Predictive analysis
Response automation
Compliance optimization
Machine Learning
Business LOG leverages the potential of Machine Learning to revolutionize enterprise log management. One of the main benefits of this technology is the ability to detect anomalies in user accesses by comparing them with the predictions of the learned model. This enables early identification of suspicious or noncompliant behavior, significantly improving the security of the company's IT infrastructure.
Detection of anomalies
Automation and efficiency
Continuous learning
Request a quote now
Request a Business LOG quote parameterized to your organization's actual needs.
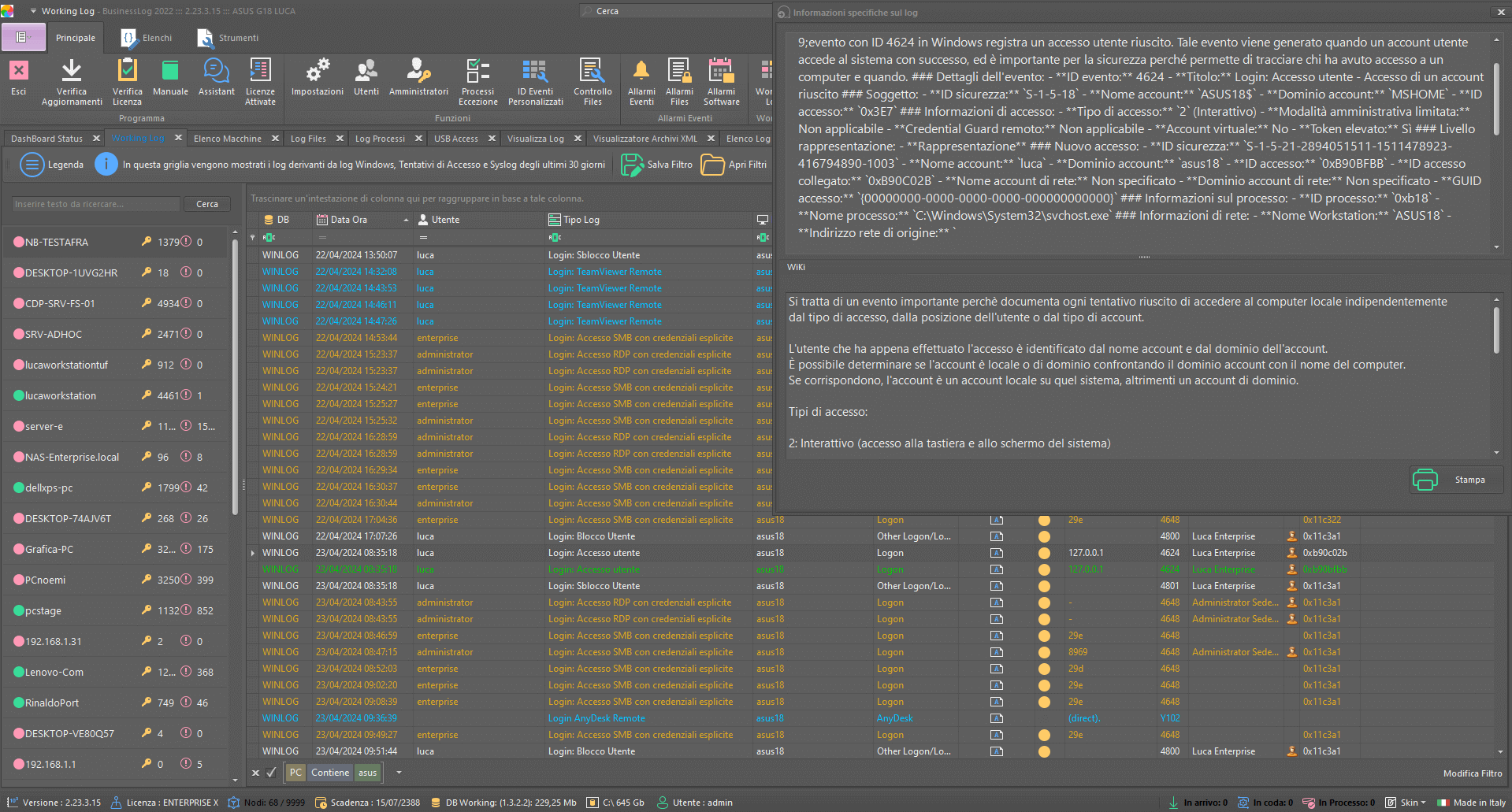
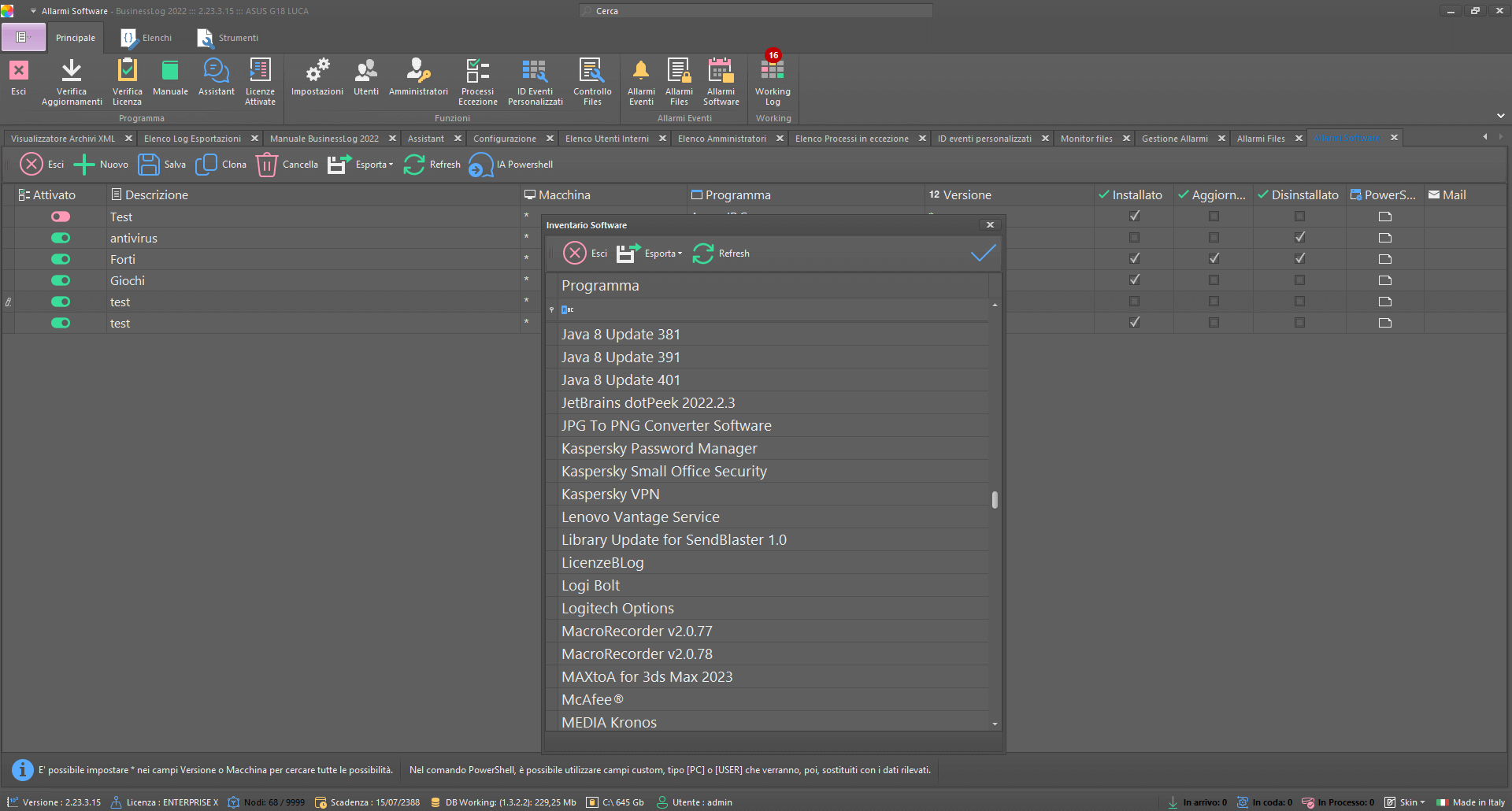
Custom alarms
With Business LOG, you can configure one or more alerts that are triggered when predefined events occur on files, folders, software, or user-defined custom events.
Alarms on files
Alarms on folders
Alarms on softwares
Alarms on custom events
Maximum compatibility
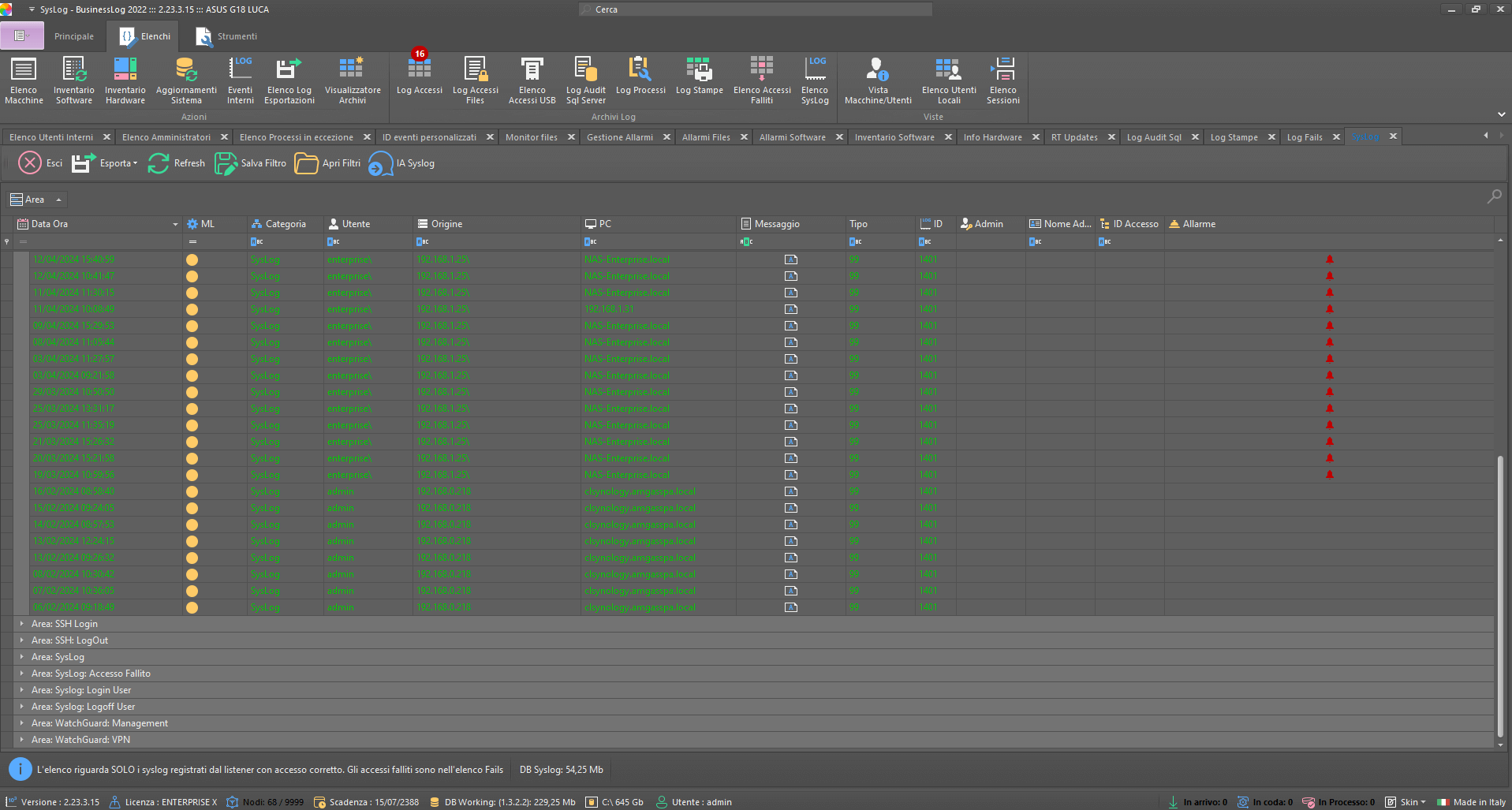
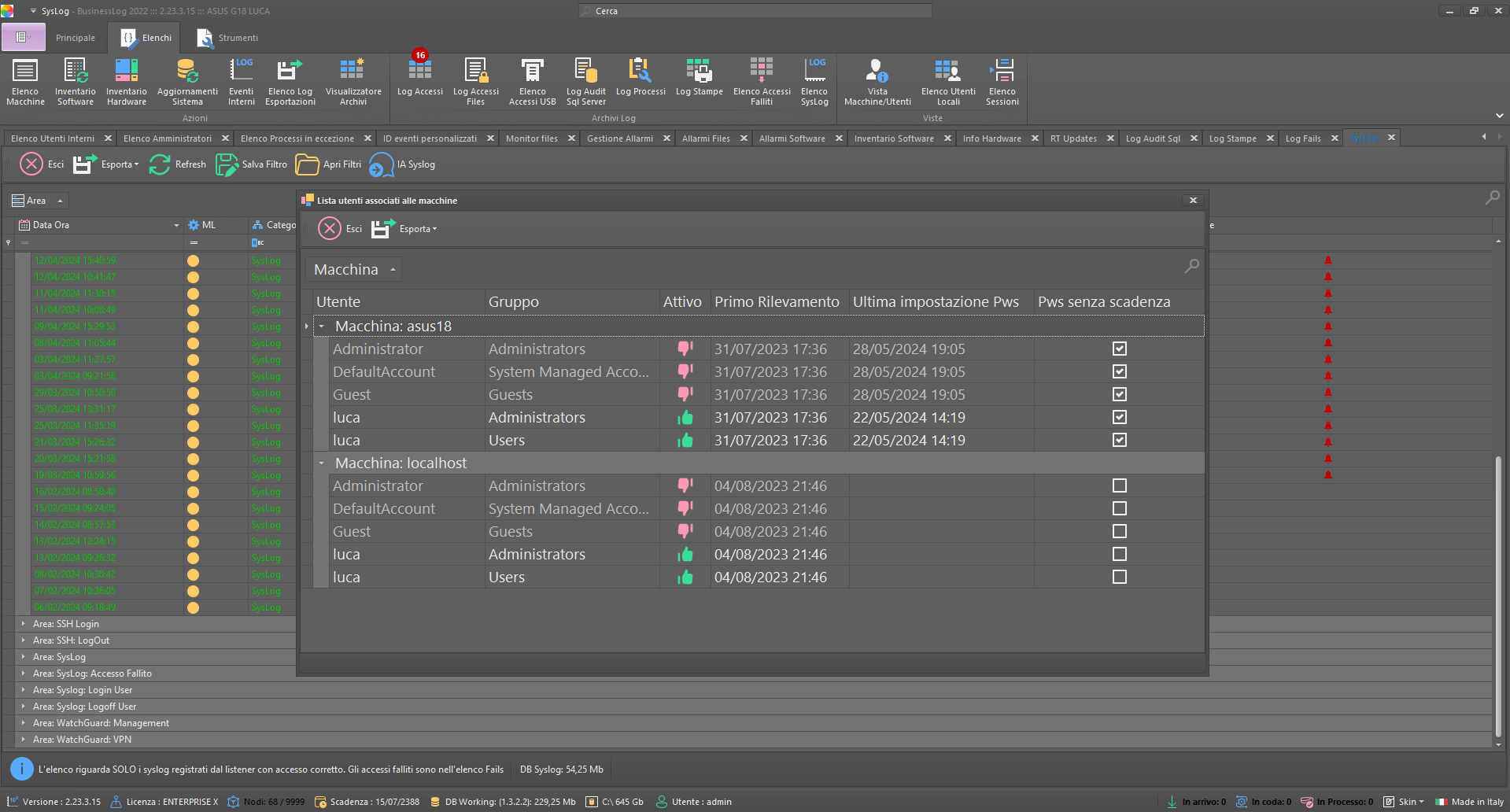
Business LOG can collect logs from all major operating systems and compatible syslog devices.
MacOS
Linux and Unix
Microsoft Windows
Syslog Devices
Request a quote now
Request a Business LOG quote parameterized to your organization's actual needs.
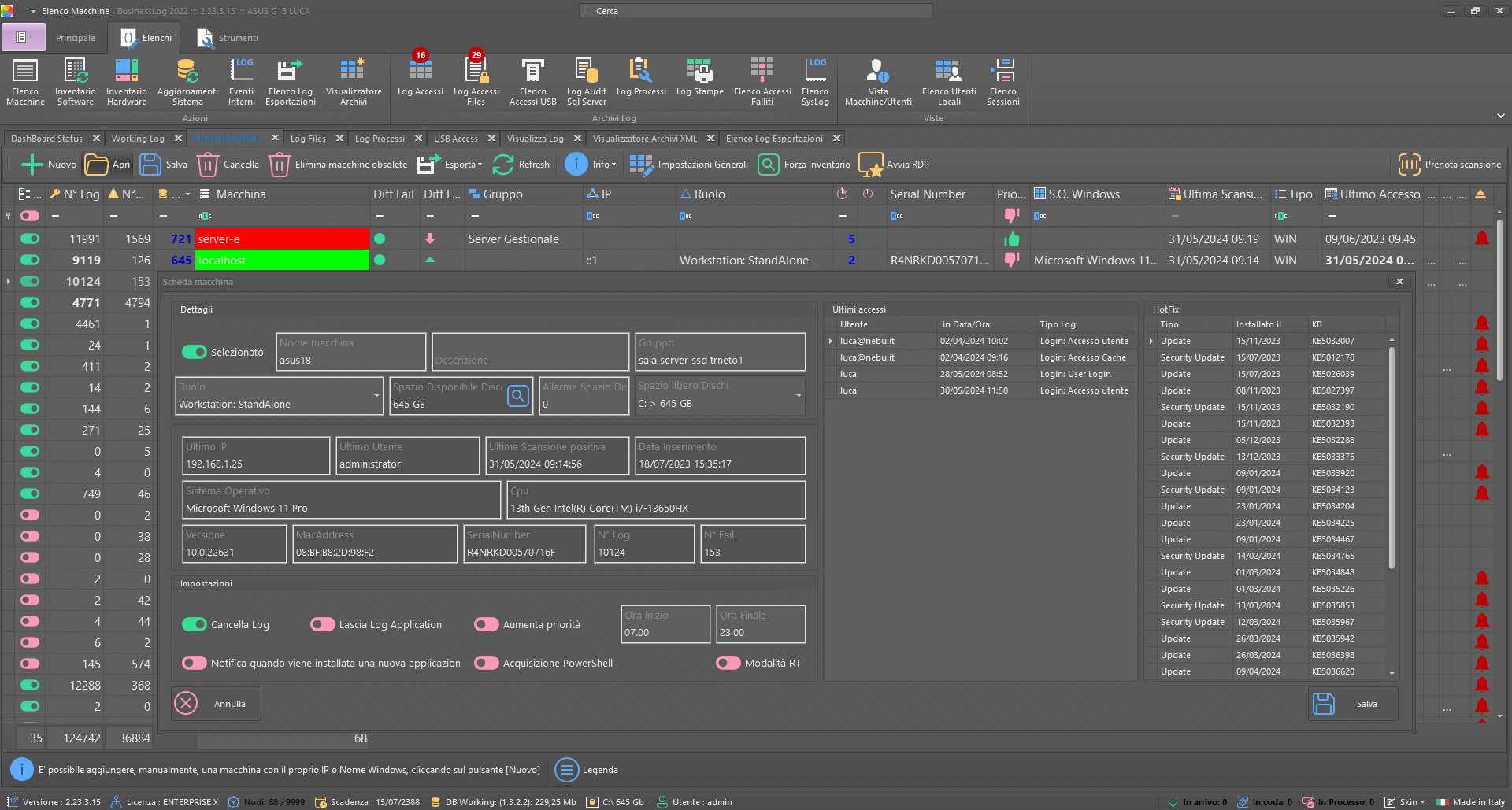
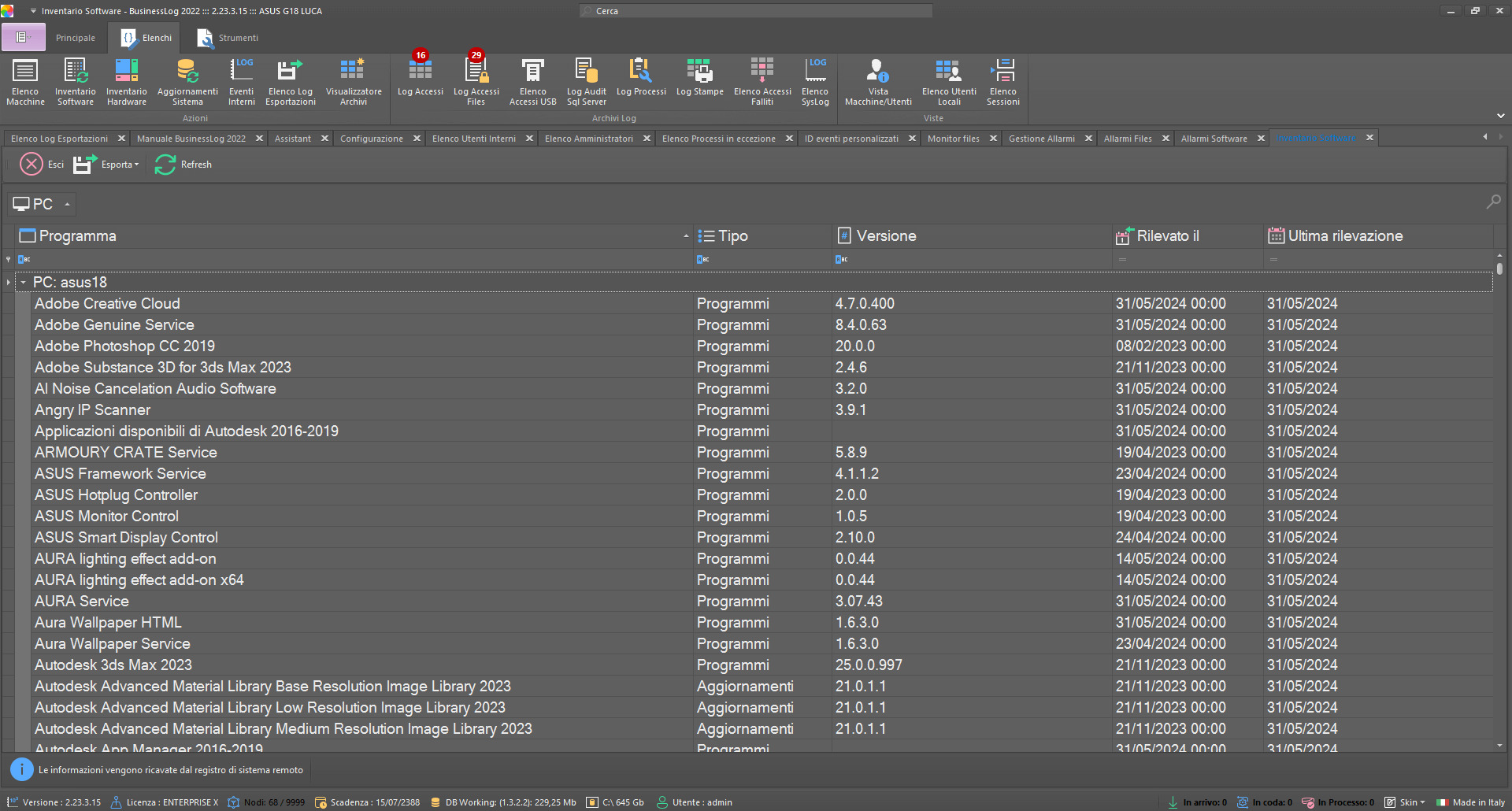
Automatic inventory
Business LOG automates the inventory of your organization's digital assets, enabling operations such as historicizing, exporting, and analyzing business-specific assets.
Machine list
Hardware Inventory
Software Inventory
Machine tab
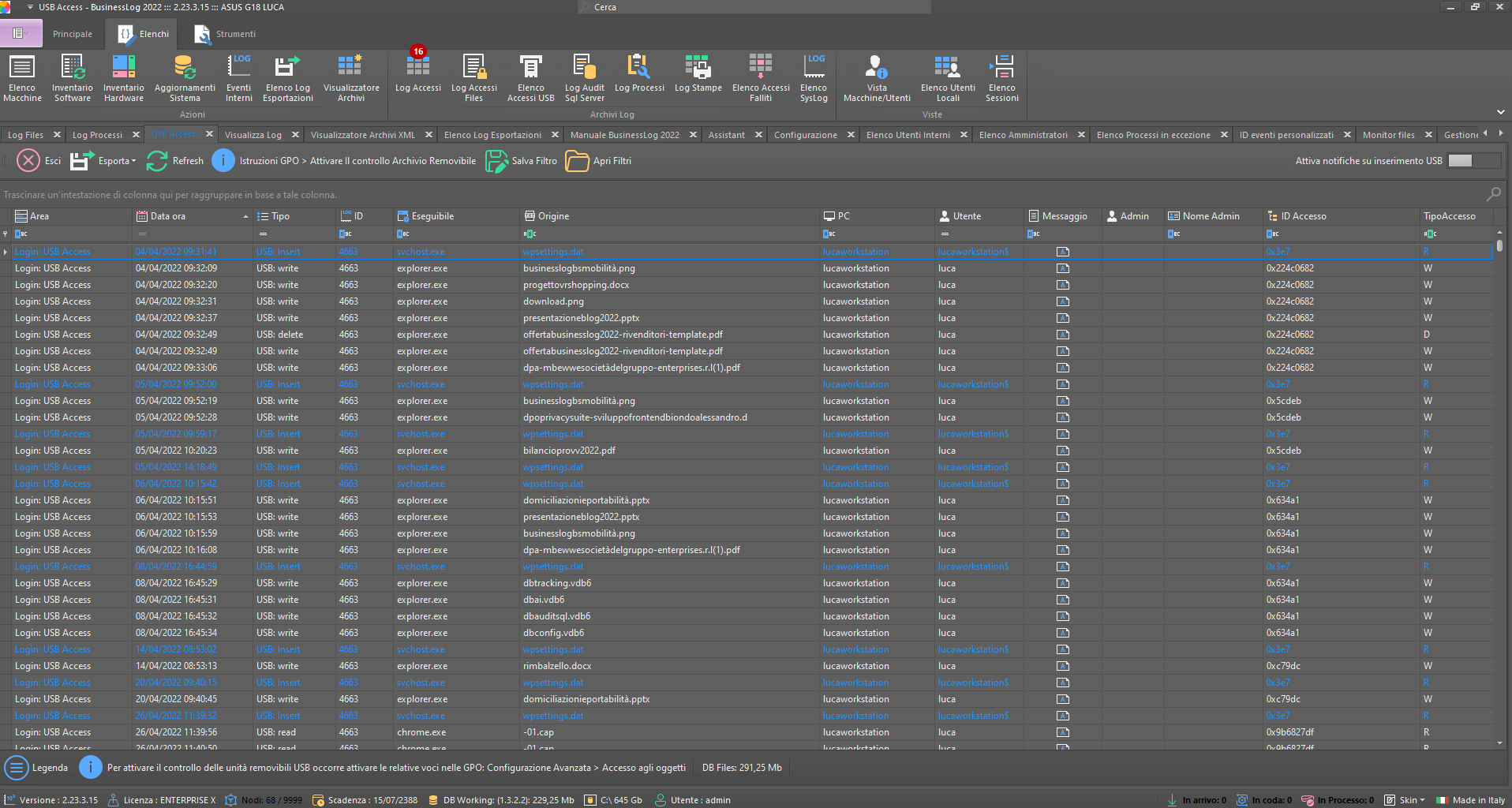
USB and Removable Disk Audits
With Business LOG, access to USB devices and removable disks can be monitored, allowing fraudulent activity to be detected and errors or critical issues to be prevented within the organization.
Monitoring fraudulent activity
Prevent and correct errors
Identifies the computers and users performing the operations
Unavoidable control
Business LOG offers seamless integration with leading software on the market, providing seamless log management. This extended compatibility allows data from different platforms and applications to be collected, analyzed and monitored, improving the organization's operational efficiency and IT security.
Receive real-time notification upon the occurrence of any custom event set by the user on the Business LOG Bot Telegram channel.
Integration is quick and easy to set up directly from the Business LOG Dashboard.
Business LOG collects logs from Teamviewer (remote assistance software).
Within the Suite, custom alarms can be configured for TeamViewer-related events.
Business LOG collects logs from Anydesk (remote assistance software).
Within the Suite, custom alarms can be configured for Anydesk-related events.
Business LOG collects logs from Supremo (remote assistance software).
Within the Suite, custom alarms can be configured for Supremo-related events.
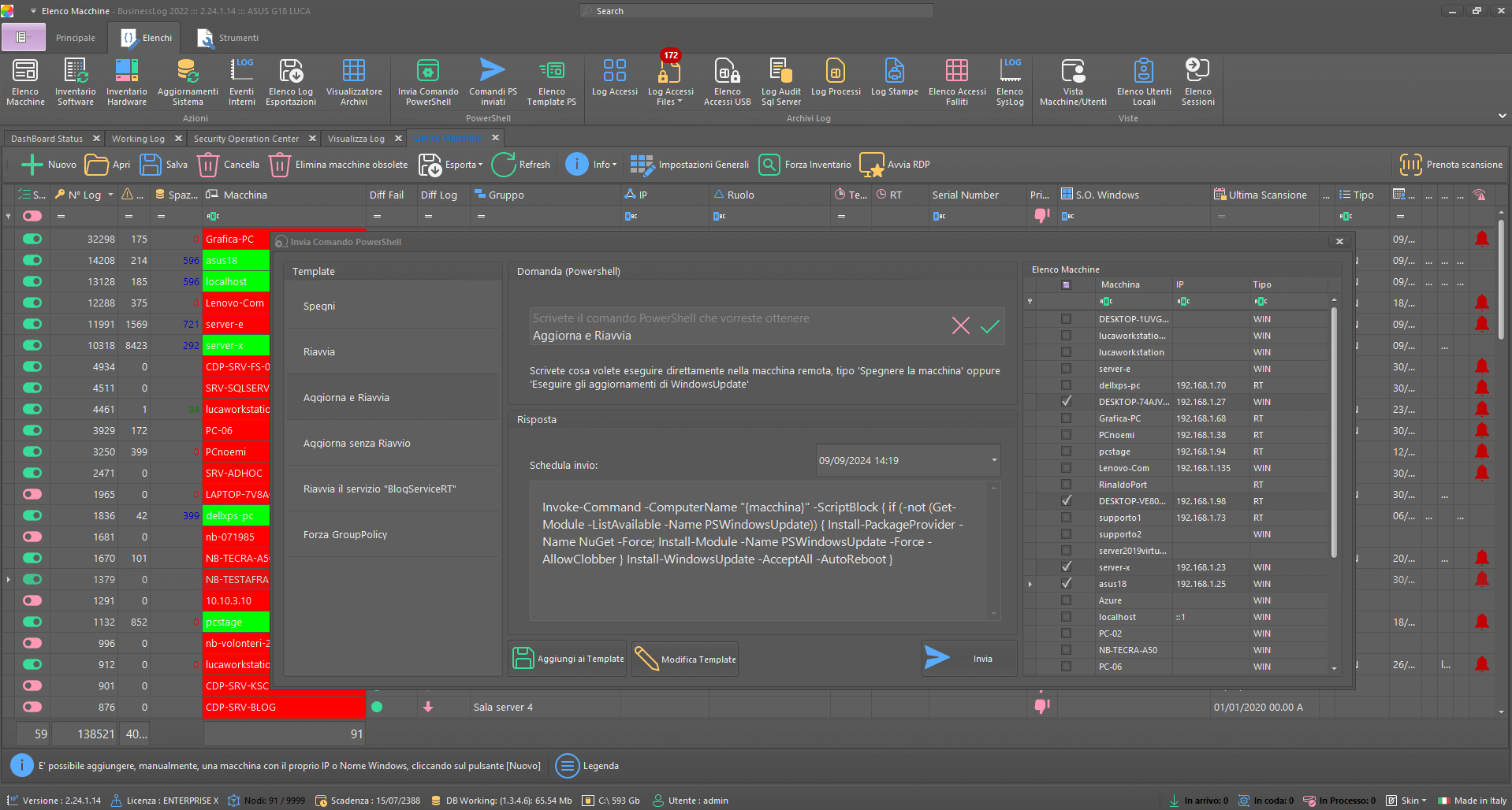
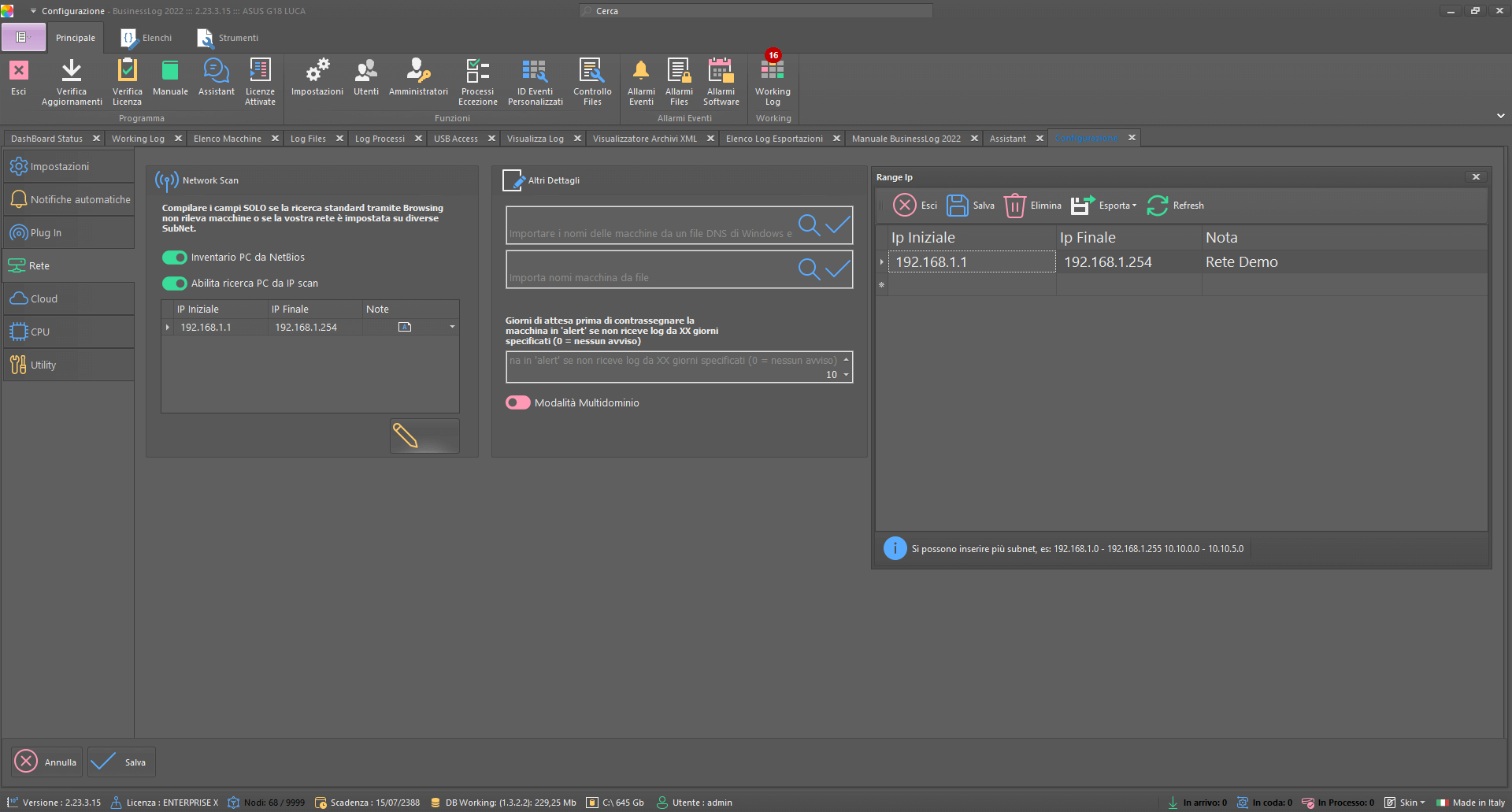
Business LOG Server enables server-level capture without the use of agents or external services on all machines in the corporate structure in the domain.
The configurable nodes in the system do not require the installation of any agents, facilitating the configuration and management of infrastructures of any size, from the smallest to enterprise-level architectures.
Log collection is centralized within a machine used as a Log Box (the machine chosen can be either physical or virtual).
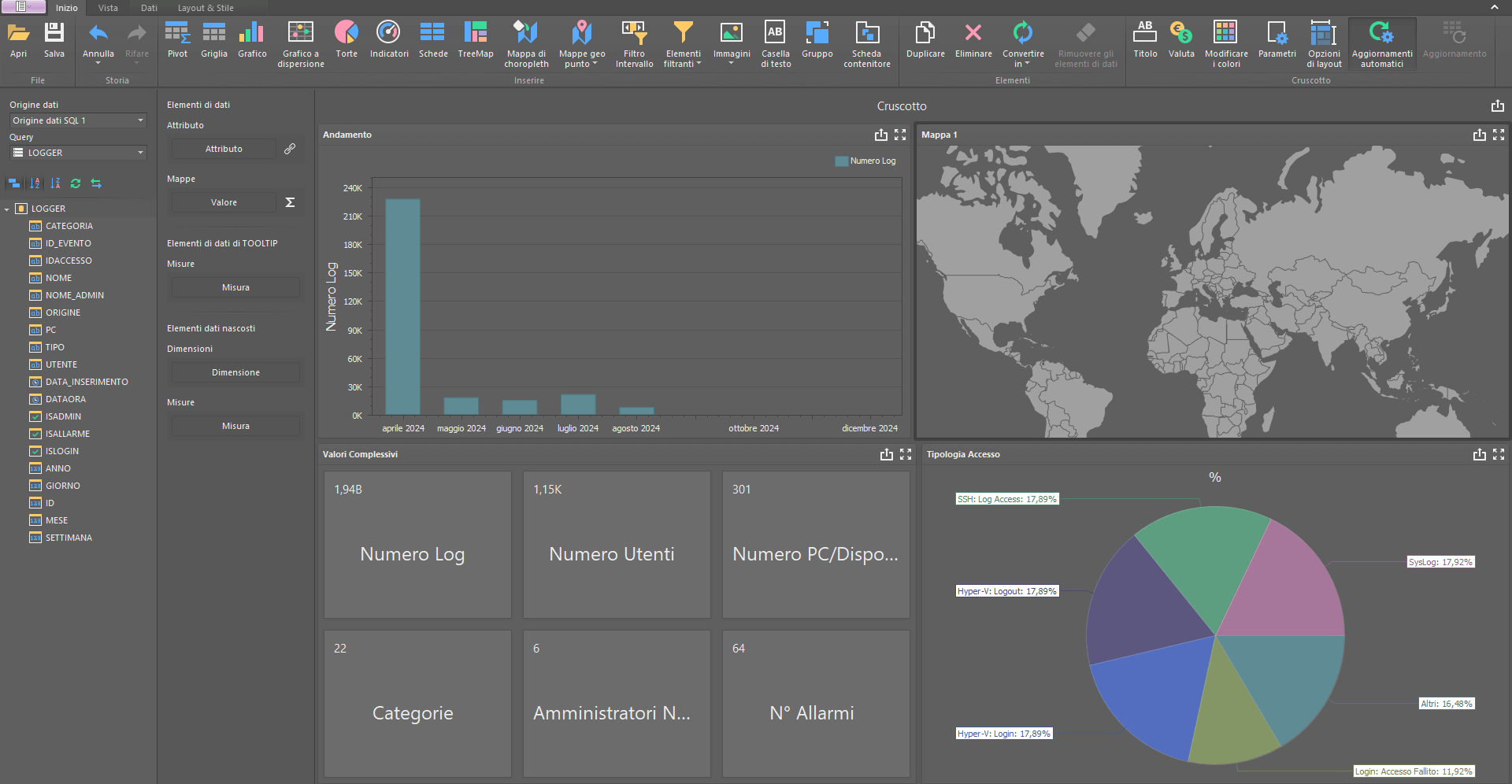
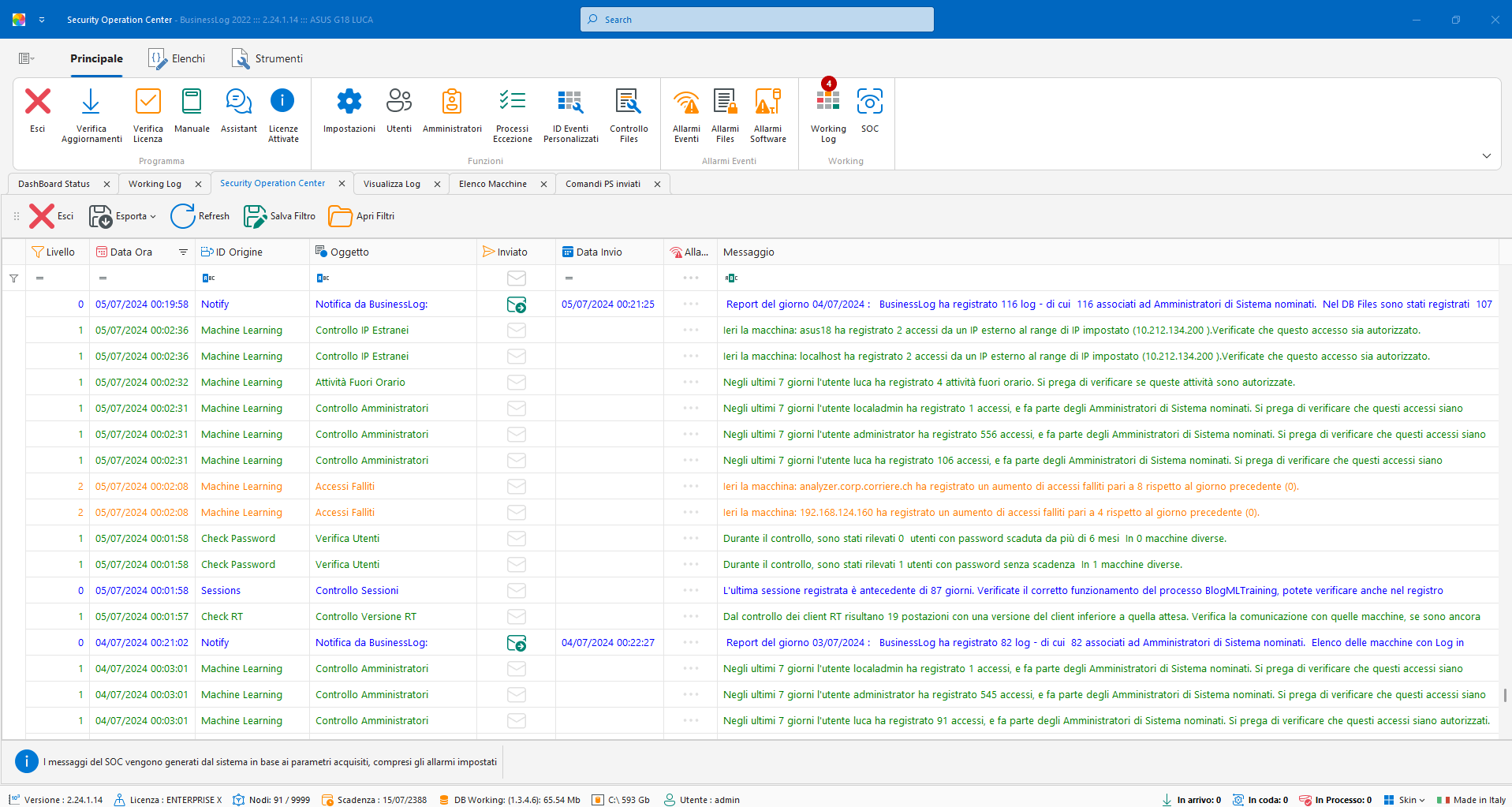
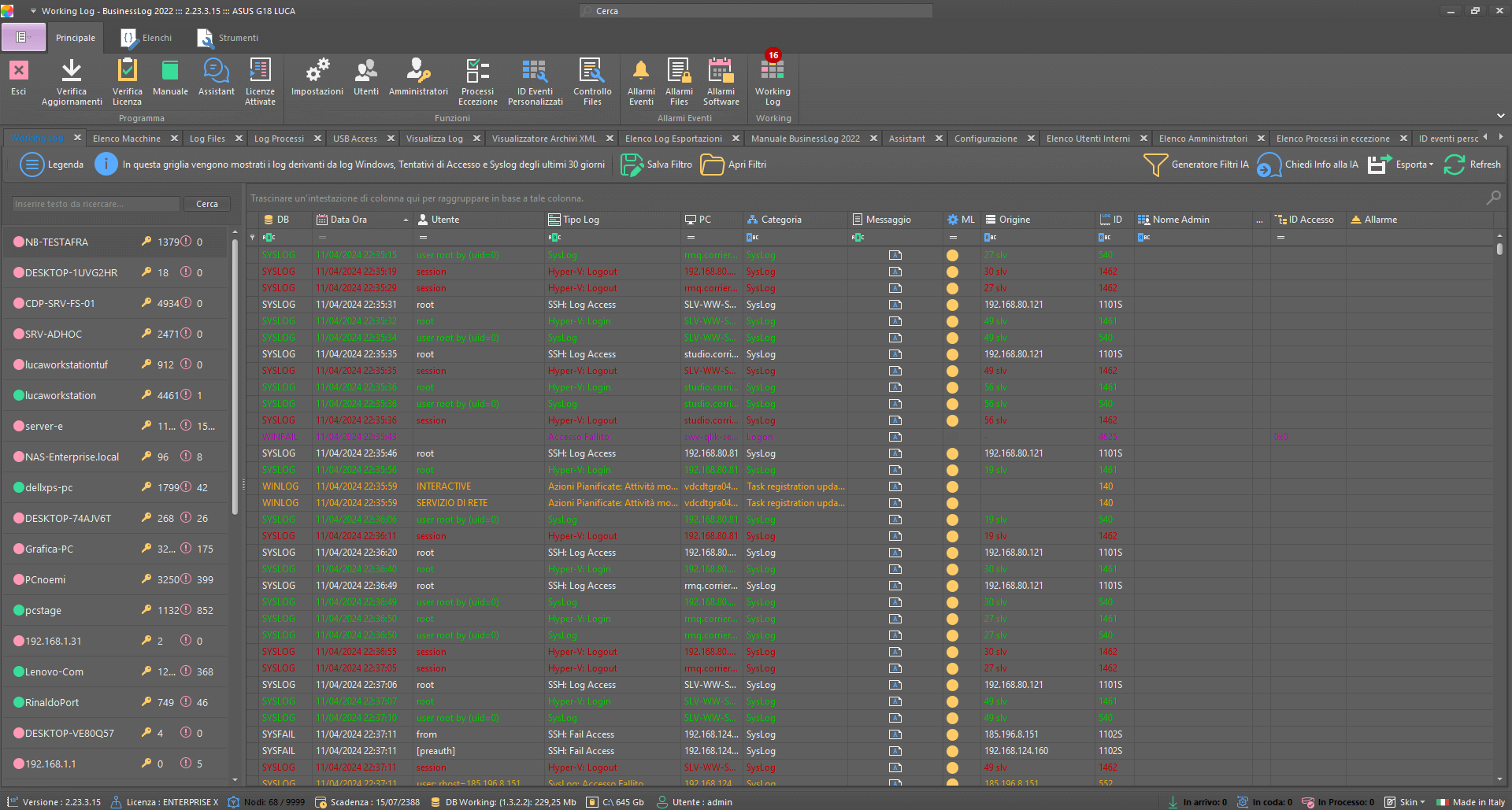
Control Dashboard
Digitally signed logs
Event management
File activity
Syslog Access Logs
Process logs
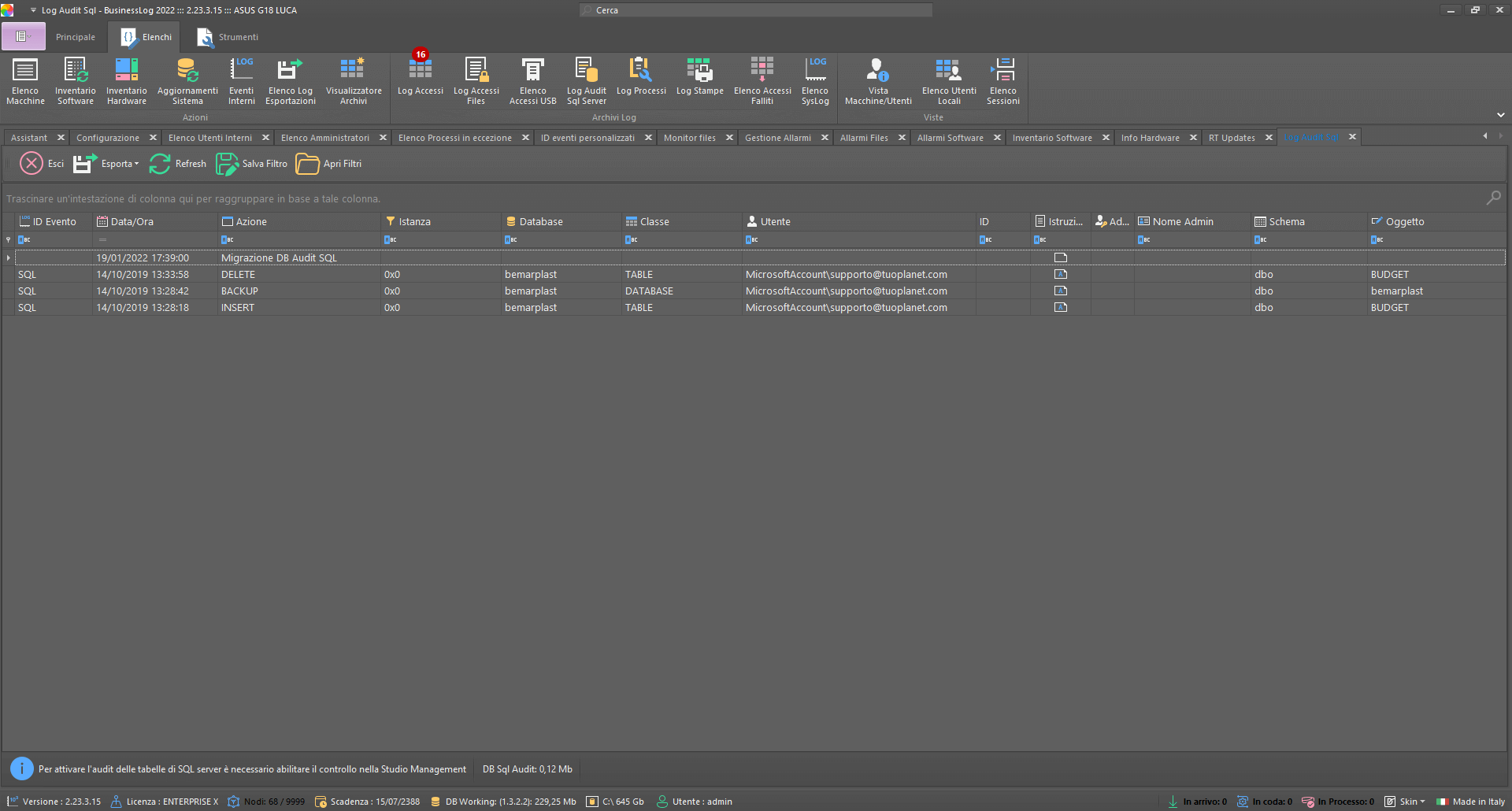
SQL log audits
Advanced statistics
Telegram integration
Available versions of Business LOG Server
Discover all the available versions of Business LOG Server.
Business LOG Plus
Records from 1 to 39 nodes (machines/devices).
Business LOG Enterprise80
Records from 40 to 80 nodes (machines/devices).
Business LOG Enterprise150
Records from 81 to 150 nodes (machines/devices).
Business LOG Enterprise250
Records from 151 to 250 nodes (machines/devices).
Business LOG Enterprise500
Records from 251 to 500 nodes (machines/devices).
Business LOG Enterprise750
Records from 501 to 750 nodes (machines/devices).
Business LOG Enterprise1000
Records from 751 to 1000 nodes (machines/devices).
Business LOG EnterpriseX
Unlimited nodes (machines/devices) and all plugins included.
Business LOG Data Center
Multi-tenant version for managing multiple Business LOG licenses.
Available plugins of Business LOG Server
Learn about all available Business LOG Server plugins.
SOC Stream Plugin
Through the SOC Stream Plugin, information collected by the SOC (installed on-premise) can be accessed on a dedicated Web site, thus ensuring a complete, always available, real-time view of security and compliance activities.
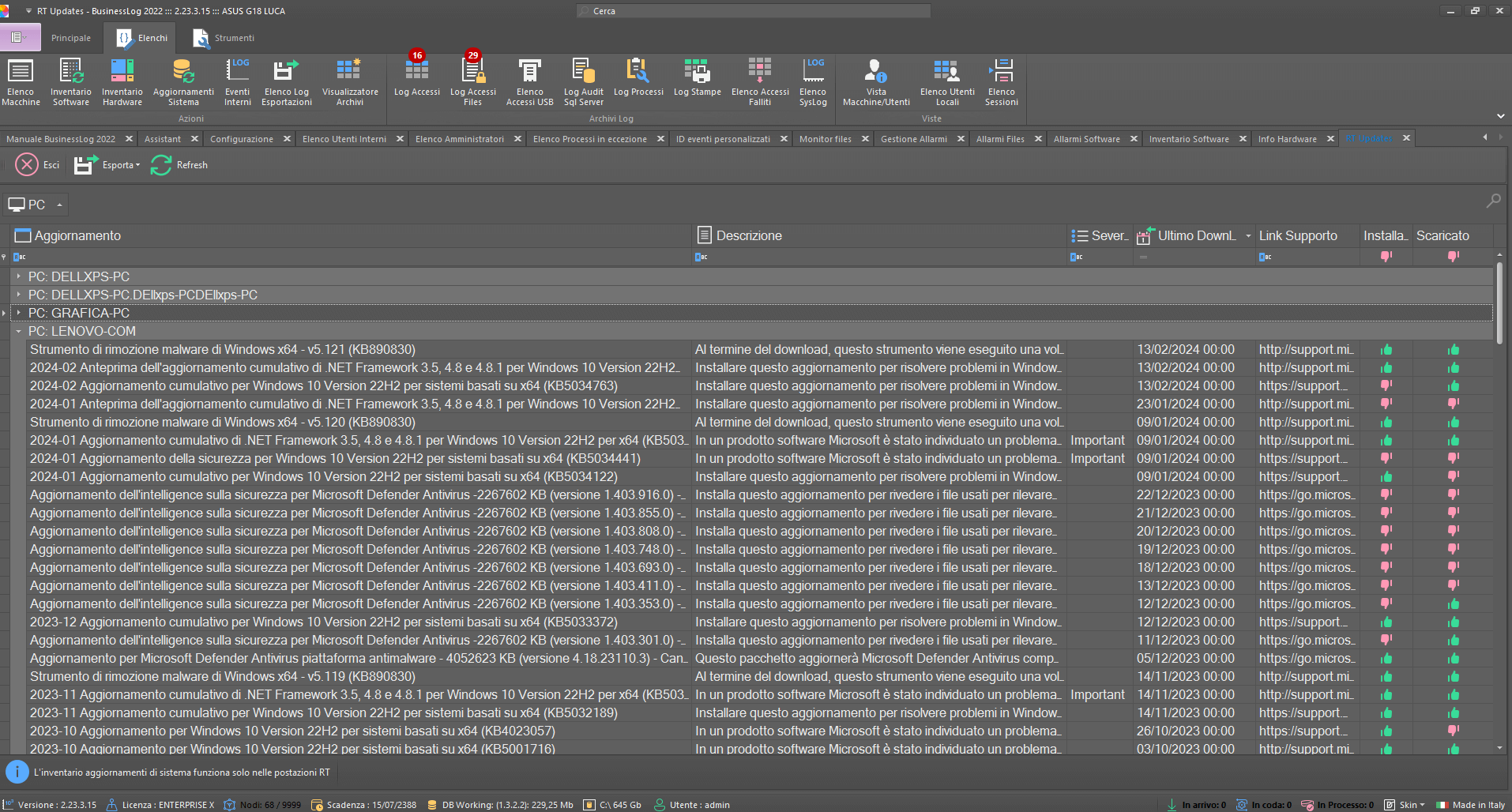
Windows Updates Plugin
Controlled machines will receive, in a special list, all listed, downloaded and installed Windows Update updates. In addition to updates, all HotFixes applied will also be reported.
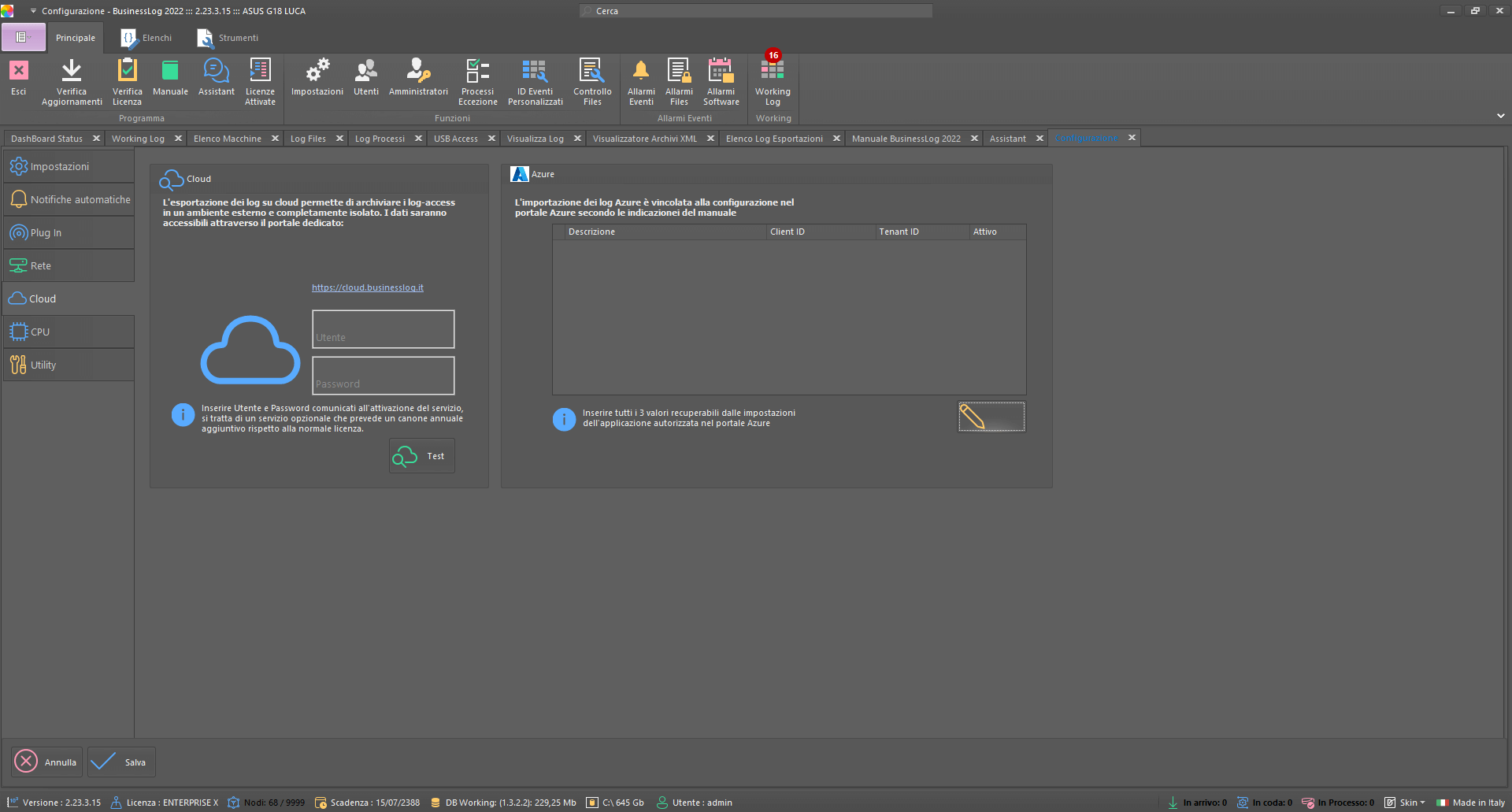
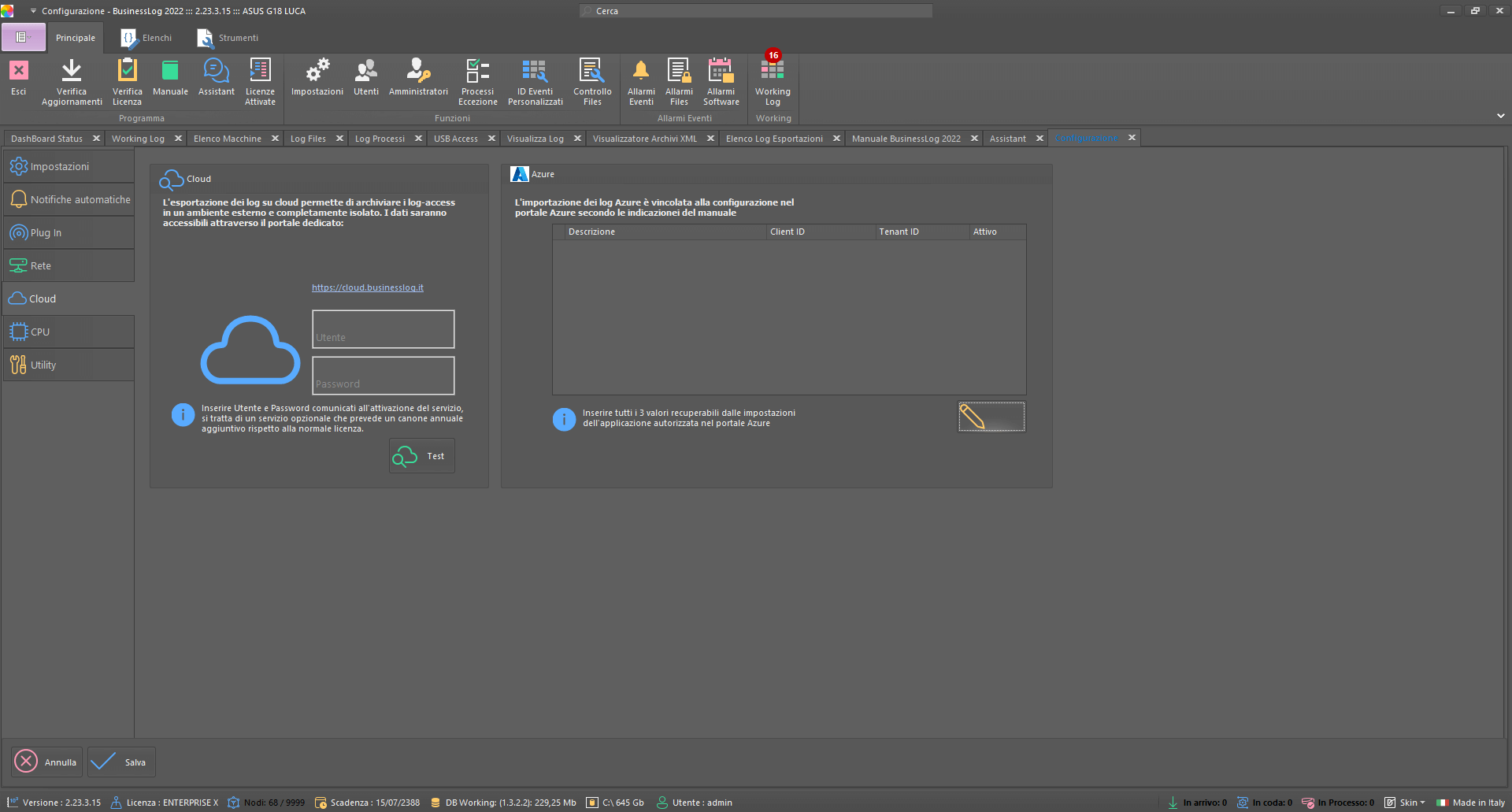
Azure Plugin
Through the Azure Plugin it is possible to log access logs from Azure Accounts. The Plugin also allows you to receive logs from Microsoft 365 (you must have an E5 license to get SharePoint logs).
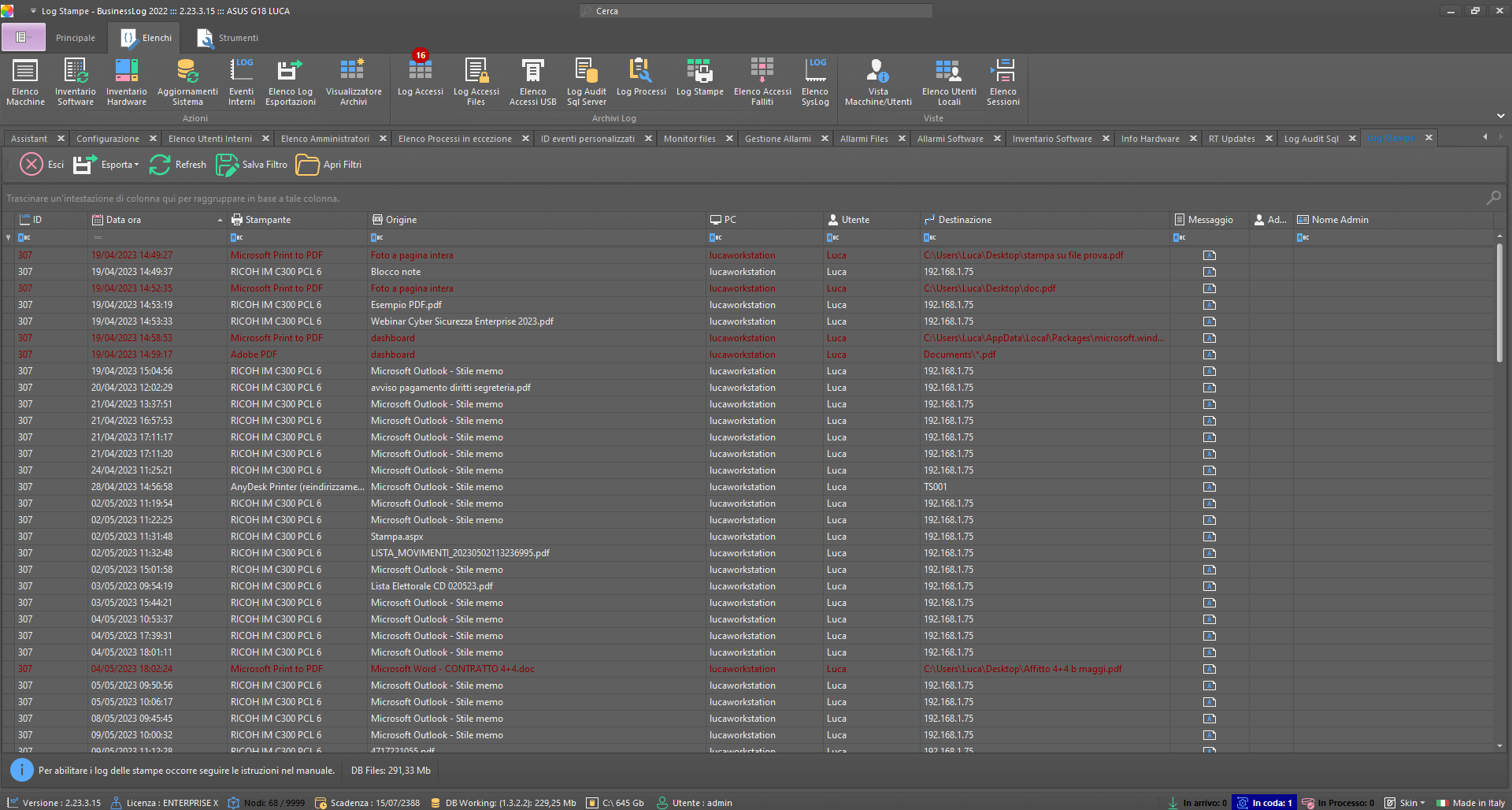
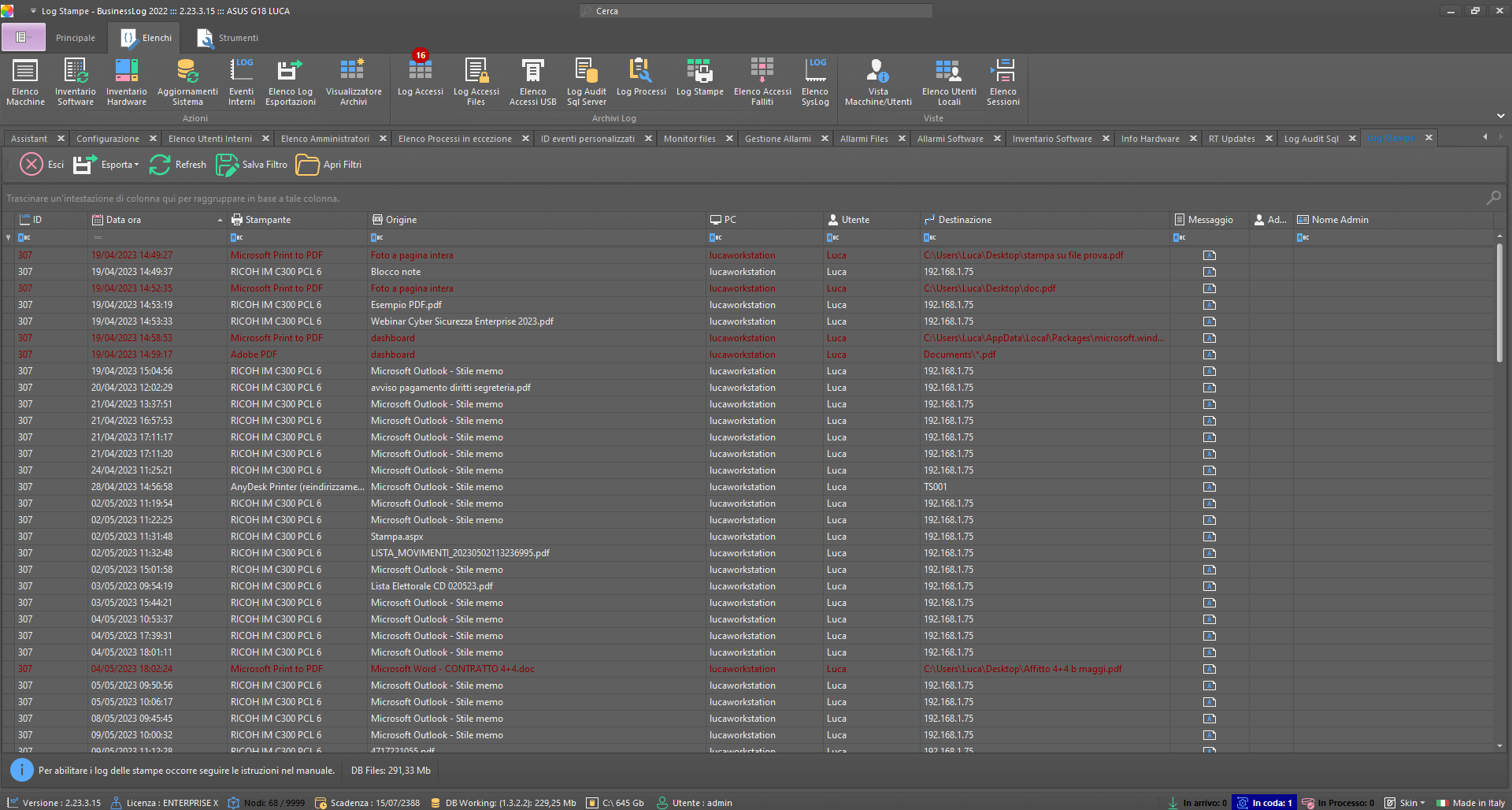
Printers Plugin
The Printers Plugin allows you to monitor all the printers within the corporate network and to be able to consult, in the appropriate table, all the print orders executed.
RT (Real Time) Plugin
The Plugin enables real-time dialog with the central server, regardless of domain. Example: log collection from off-domain Windows machines and in real-time.
Backup Logs in Cloud Plugin
The Log Backup Plugin in Cloud allows you to export logs to a private cloud storage (available via web in Microsoft Azure or through dedicated application).
USB Plugin
The USB and Removable Disk Plugin allows you to monitor the insertions, readings and writes of removable disks (USB sticks, external disks or SD/microSD).
AS400 Plugin
The As400 Plugin allows you to collect and integrate logs generated by IBM As400 machines directly into Business LOG.
SQL Plugin
The SQL Plugin allows to acquire logs from the advanced audit of SQL server and get information about queries in use in database tables.
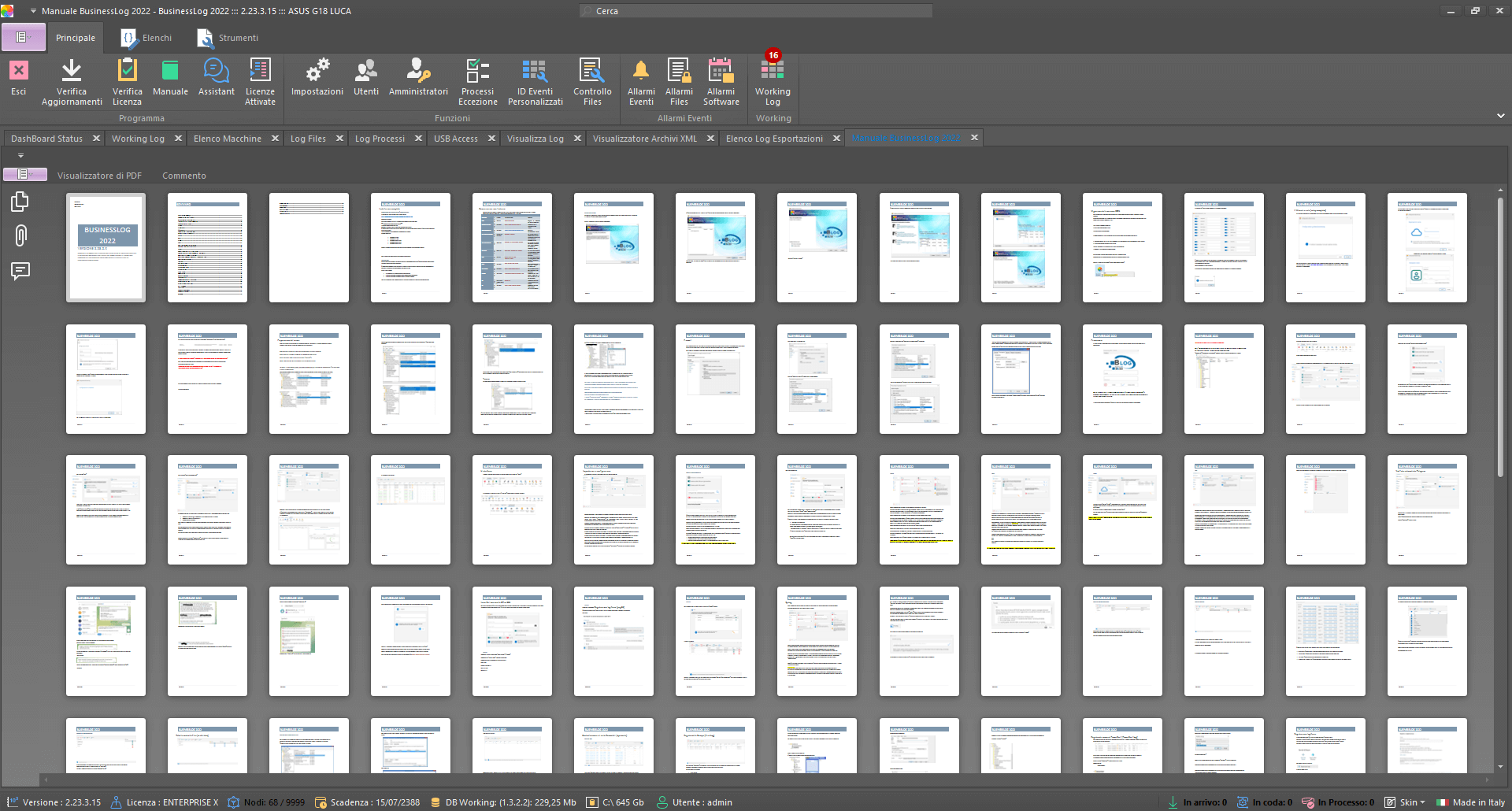
Find out the minimum requirements for Business LOG Server versions.
Up to 39 nodes.
Over 40 nodes.
Find out all the key answers about Business LOG Server.
Request a Business LOG Quote
Are you interested in the Suite? Request a Business LOG quote now to evaluate the opportunity for your organization